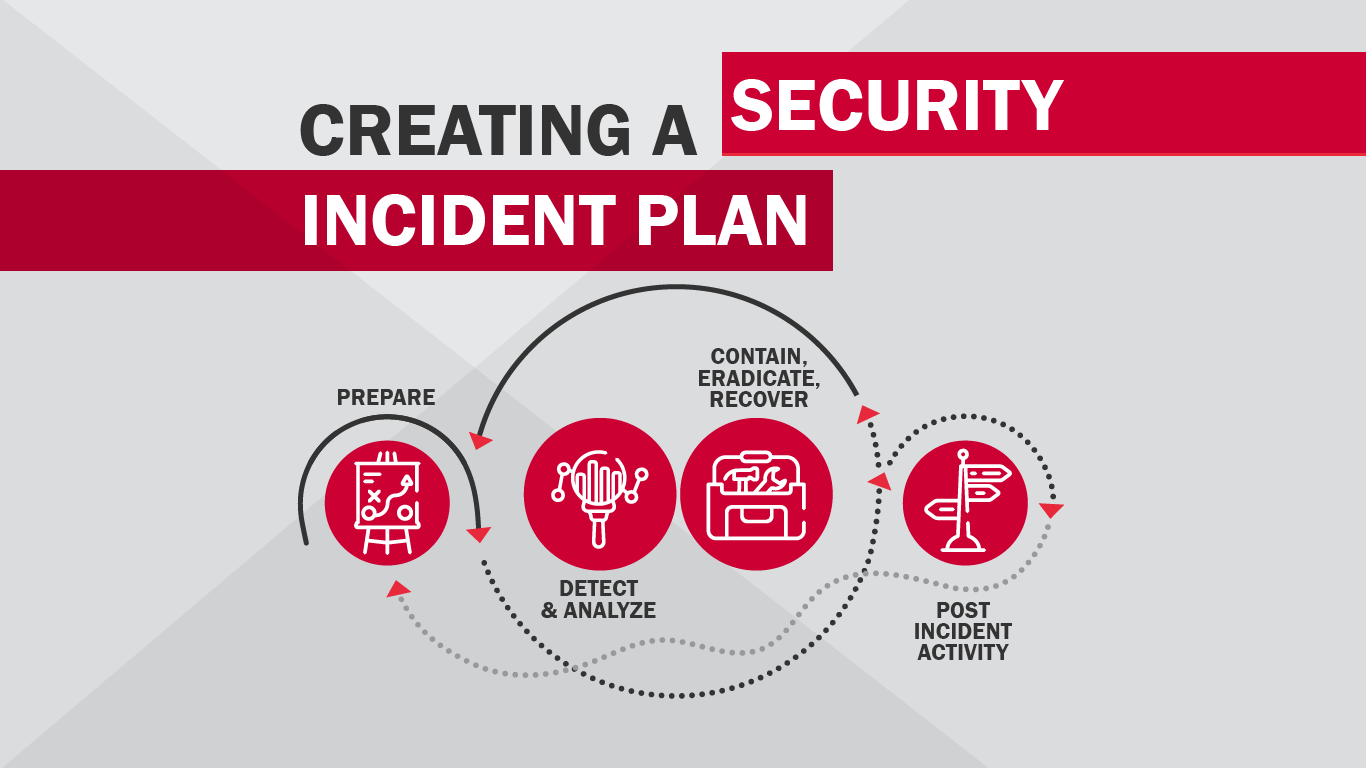
We don’t have to tell you that neglecting to prepare before an inevitable incident can have disastrous consequences. There’s no on-the-spot decisions you can make that wouldn’t be better if made thoughtfully ahead of time. What’s more, it’s easy to make silly blunders and bad decisions under pressure. Handling a security incident is a complex affair, and this article is by no means a comprehensive guide to creating your plan, but we can provide a few tips to help set your plan in motion.
Create a security incident response policy and plan.
Don’t be the business that hasn’t gotten around to it. Your plan doesn’t need to be a novel, but it is important to start somewhere. Start by creating a security incident response policy that includes a definition of what you consider to be an incident, the organizational structure for responding to an incident, roles and responsibilities of your response team, and reporting requirements. You can then use your policy to develop a response plan based on the items in your policy.
Determine your incident response team.
You will need to determine who is responsible for responding to an incident and what their roles are. You will also need to make sure that everyone within your organization knows who to contact in the event of an incident. You should create and distribute a contact list of those on your response team, their roles within the response team, and how to contact them.
So now that you know you need a response team, how do you choose who should be on it? First of all, you’ll need to determine whether you have the resources to create a team with only employees of your organization, or if you will need to supplement your resources by outsourcing some responsibilities. You also need to consider the expertise of those you select for your team. They will need specialized knowledge and experience such as intrusion detection, vulnerabilities, exploits, and other aspects of security. Members of your team also need to be available to respond to an incident at any time, even outside of normal business hours. You may also need to include individuals outside of your organization including legal representation, law enforcement, public affairs, facilities management, etc.
Determine your containment strategy.
Failing to quickly contain the threat can result in your resources being overwhelmed, causing additional damage that could have been prevented. Containing a threat gives your business valuable time to develop a solid remediation plan, but it’s important that you pre-determined procedures for containment rather than implementing them on the fly. Containment strategies should vary depending on the type of incident. When you develop your containment procedures, you should create a separate strategy for each major type of incident. You’ll need to consider various criteria including potential for damage and theft, for evidence preservation, service availability, as well as the time and resources needed.
It can be useful to observe the attacker to be better prepared to defend against future attacks. Organizations will do this by directing the attacker to a sandbox where their activity is contained but they can continue to monitor their actions and gather evidence. It’s important to never simply observe the bad actor performing their attack without directing them to a sandbox, otherwise you could be liable for failing to contain them should they use your compromised system to attack other systems.
Pre-distribute contact cards.
Be sure not to rely on your regular methods of communication to spread the word of an incident. Your phone lines and email system can be interrupted due to an attack, leaving people to scramble to figure out how to contact each other. Create cards that outline who to contact during an incident and be sure to include their cell phone number. To avoid confusion, it’s a smart idea to list one or two people as the initial points of contact; they can then notify all others who need to get involved in responding.
Gather evidence and report to law enforcement.
A common reason cyber-criminals are never held legally accountable for their crimes, is that organizations forget to gather evidence in the heat of the moment. Another common reason is law enforcement is never properly involved. Your incident response team should make a point of becoming familiar with their law enforcement resources. It’s important to determine beforehand which types of incidents can be reported, how to report them, what evidence should be gathered, and how to collect that evidence. It’s a good idea to appoint one individual on your response team as the main point of contact for communicating with law enforcement.
Get your users involved.
Your IT team can’t do it alone. The goal is to keep incidents from happening in the first place, and that requires buy-in from all the users on your network. Make sure you have acceptable use policies in place so that users know how to help protect your network. It’s also important to provide training for how to spot and avoid attacks.
Get help if you need it.
If you lack all the resources and expertise you need to create and execute a solid incident response plan, you shouldn’t hesitate to supplement your weak spots with outside help. Les Olson IT has a large team of IT experts that can help you maintain your network security and respond in the event of an incident.